
Due to their regular dealings with personally identifiable information (PII), law firms should take measures to reduce the chances of a data breach. PII can be used to identify, contact, or locate a single person or identify an individual in context. In the hands of wrongdoers, PII can be used for identity theft, fraud, or simply be sold to someone else who can be more creative.
It is extremely important to acknowledge that law firms are, in fact, PII repositories that have access to information such as names, birthdates, Social Security numbers, addresses and state identification numbers. It would be very naïve to believe that a data breach could never happen to your firm.
Maybe your firm is smaller or less known than others, but studies have shown that as many as 1 in 4 firms have been victims of a data breach. This data should encourage you to consider “a worst-case scenario” and develop a plan for protection. Always take the extra step to ensure that you are doing your part in keeping your information and your clients’ information safe. This post will give an overview of some of the simplest things that you can do to keep potential hackers at bay.
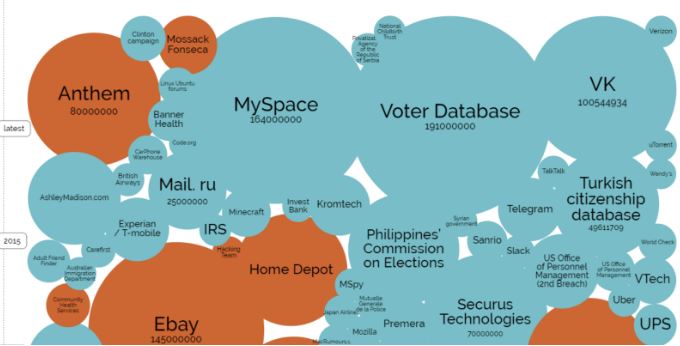
Latest data breaches, informationisbeatuful.net
Cloud Services
If your firm isn’t large enough to have a dedicated IT staff who can manage its infrastructure, or if a full time IT position isn’t in the budget, cloud services are an excellent way to get professional IT services at a fraction of the price. A cloud service is any resource that is provided over the Internet.
In a traditional scenario, users would install software on their computers and save documents locally on their hard drive. Although common, this scenario is prone to various problems. Hardware is susceptible to failure, and not using best practices when it comes to security may leave your data vulnerable. Cloud services typically have an entire team of engineers who dedicate their time to developing a service that is fast, secure and reliable. Storing documents in the cloud allows you to access them whenever and wherever you choose. This also eliminates workflow pitfalls such as forgetting your laptop, or worse, losing it or having it stolen. Services such as Dropbox, Google Drive and Microsoft OneDrive are all excellent examples of free cloud storage. For larger firms, you may rent or lease infrastructure components, such as servers, for a fraction of what it would cost to actually purchase the hardware and have it configured and maintained. In terms of security, when using a cloud-based service, the responsibility for keeping your data safe now shifts from your firm to a third-party. This does not mean that the risk of a data breach is eliminated, but it is considerably lessened.
Password Management
Despite the importance of passwords in a business environment, bad practices are still heavily prevalent. Various tools can be used to crack passwords, but they aren’t entirely necessary if users fail to do their part to protect themselves through the use of password management.
As a basic rule of thumb, passwords should never be written down and kept in an obvious location. Great examples of what not to do include passwords written on sticky notes on monitors or underneath keyboards. Although in these instances someone would have to be physically present to obtain this information, it is best to be cautious and assume that anyone could compromise your information.
Login Security
Utilizing these tools can eliminate the risk of someone rummaging through your email and personal data completely undetected:
Two-factor authentication- the use of another authentication method in addition to a password. Login tracking – receiving notification when someone logs into your account; or keeping record of the locations where your account logs in from.
Password Strength
Brute forcing is an attack which is aimed at weak passwords that lack complexity. The method includes trying to guess every possible combination until one works.
To avoid this, many sites and services use password policies. These policies serve as a template, which assist users in creating strong efficient passwords. Normally they recommend a password to be a certain length and use a variety of characters such as upper and lowercase letters, numbers and symbols. The idea is to make a password as complex as possible, so although the password “Password1!” meets all of the requirements, it doesn’t necessarily mean it’s secure.
Because of this, passwords have now evolved into passphrases which use a combination of words instead of one. When choosing a passphrase, it’s important to choose something memorable and personal, such as combining the name of your favorite food with your favorite actor,D!c@pri0Pizz@.” But, try to avoid common phrases such as song lyrics or famous quotes, as these may be easier for someone to guess.
As a last tip, it’s good to get into the habit of changing your passphrase at least once every 90 days. This ensures that anyone who is able to obtain it can only use it for a limited time.
Entire books have been dedicated to detailing ways in which email can be used maliciously. From an attacker’s standpoint, having access to a direct email address could allow them to target someone directly. In 2015, an American network technology company named Ubiquiti Networks Inc. reportedly lost $46.7 million because of a spear phishing email. Unlike regular phishing, where fraudulent emails are sent to several recipients, spear phishing involves targeting someone directly.
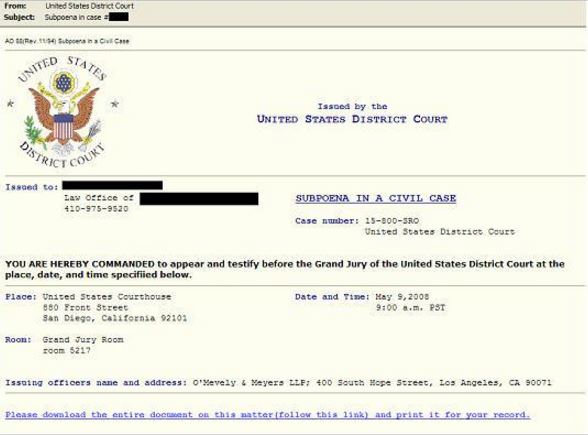
Spear phishing email, NY Times
In the above example, thousands of executives around the country were sent an email appearing to be an official subpoena from the U.S. District Court in San Diego. The email included the executive’s name, company and phone number. In order to obtain further details about the subpoena, the recipient was to download the document. Unfortunately, the download link installed a RAT (remote access Trojan) which recorded keystrokes and gave access from the victim’s computer to the attacker.
You should always be wary when it comes to following links or downloading attachments from emails. Always keep an eye on the “from” email address and verify it is from a trusted source. If an email seems to be generic and makes indirect references to you or your firm, and addresses you by “user,” “customer,” or “member,” instead of by name, there is a good chance you’ve encountered a phishing email. It is important to remember that companies will never ask you to disclose sensitive data through email. If ever in doubt, simply try calling the individual to verify legitimacy.
Workstation Security
The gateway to access your data is through your workstation. Whether it be a laptop or a desktop, the same basic principles apply in keeping your information safe.
- User account: Make sure that your user account is secured with a passphrase. This will eliminate the basic risk that if someone gains physical access to your machine, it won’t auto-login and have its contents made available.
- Updates: Be sure to regularly check for updates to your operating system. As new flaws are discovered, software patches are deployed to fix vulnerabilities and eliminate attack vectors. Keeping your machine updated means reducing the ways a hacker could gain access to your system.
- Wi-Fi: If using a mobile workstation, be wary about connecting to unsecure, free Wi-Fi hotspots. Malicious users can potentially look at the data that flows from your computer to the wireless router. Being on the same network as an attacker also makes it substantially easier for them to compromise your system. One of the most notorious attacks for public Wi-Fi is known as a Man in the Middle (MITM) Attack. In this situation, a user is able to reroute traffic between you and the router or hotspot. Instead it goes from you, to the attacker’s machine, to the router. As it passes through the attacker’s machine, your data can be searched for passwords, account numbers etc. The worst part is that since it goes to the router afterwards, your browsing experience is not affected and you are completely unaware.
- Antivirus: Antivirus applications do more than simply keep out viruses. Normally they come as antivirus suites that also check for malware, spyware, spam, intruders and an array of other problems. Like operating system updates, antivirus vendors like Norton, McAfee and Kaspersky regularly push out updates that keep your antivirus application knowledgeable about the most current threats. It is also important to regularly perform scans of your system to ensure that nothing went unnoticed.
- Peripherals: Curiosity is always piqued when finding a USB flash drive on the ground. We rarely think twice about plugging it into our computer to look at its contents. There are now various applications that can be installed on flash drives to make them automatically install viruses on your computer simply by plugging them in. Although it seems highly unlikely, this method was actually used to deliver one of the most intricate pieces of malware to Iranian nuclear power plants. Never plug in a foreign device to your main workstation, and always be sure to scan it for malware from another machine before use.
Conclusion
All computer users should be conscious of security principles regardless of who they are. When it comes to data security, everyone is at risk. Taking preventative measures is always the best course of action to ensure you don’t fall victim to compromise. Although risk can never truly be eliminated, being conscious of your actions and establishing best practices can certainly mitigate the chances of falling victim to a cyber threat.





